- Products
- Services
- About Us
- Support
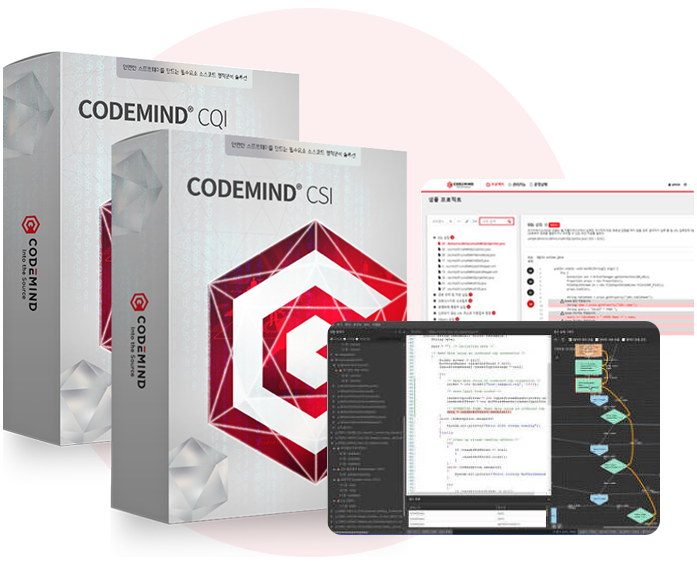
Developed with a cutting-edge technology that finds all execution paths without having to running your software, CodeMind CSI/CQI is an essential tool to keep your software safe and secure.
CodeMind CSI/CQI helps you identify security weaknesses and find and fix execution errors hidden in the software source code in advance. Utilizing the latest static analysis technology to find defects in all execution paths without executing the software, it helps you to maintain the high quality and security of the software you develop.

Detects security weaknesses according to major secure coding standards at home and abroad

Allows you to review the up-to-then results during analysis based on on-the-fly technology

Covers both security- and quality-related rules

Enhanced security
Ensures increased safety and security by detecting security weaknesses in advance

Improved code quality
Covers exhaustively exploring every possible scenario, supplementing the limitations of dynamic analysis

Reduced development cost
Reduces significant cost, time and resources required for development and defect detection and correction

Improved customer experience
Ensures your software reliability by proactively preparing for possible issues caused by software defects